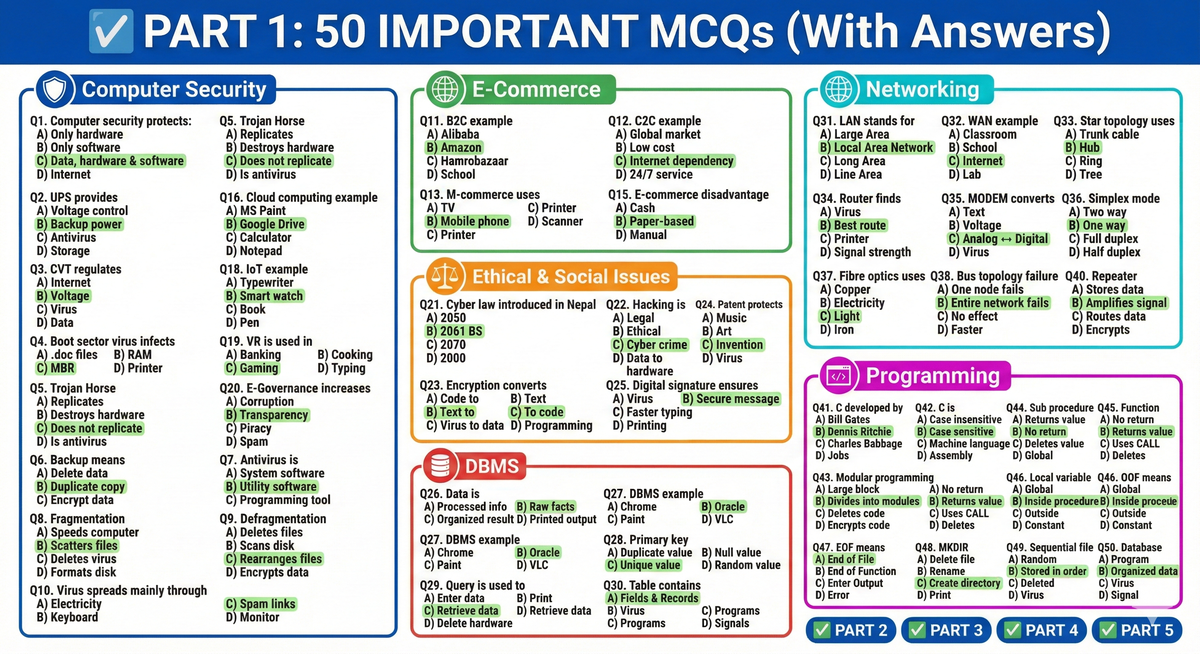
✅ PART 1: 50 IMPORTANT MCQs (With Answers)
🛡️ Computer Security
- Computer security protects:
A) Only hardware
B) Only software
C) Data, hardware & software
D) Internet
Answer: C- 2. UPS provides:
A) Voltage control
B) Backup power
C) Antivirus
D) Storage
Answer: B- CVT regulates:
A) Internet
B) Voltage
C) Virus
D) Data
Answer: B- Boot sector virus infects:
A) .doc files
B) RAM
C) MBR
D) Printer
Answer: C- Trojan Horse:
A) Replicates
B) Destroys hardware
C) Does not replicate
D) Is antivirus
Answer: C- Backup means:
A) Delete data
B) Duplicate copy
C) Encrypt data
D) Compress data
Answer: B- Antivirus is:
A) System software
B) Utility software
C) Programming tool
D) Browser
Answer: B- Fragmentation:
A) Speeds computer
B) Scatters files
C) Deletes virus
D) Formats disk
Answer: B- Defragmentation:
A) Deletes files
B) Scans disk
C) Rearranges files
D) Encrypts data
Answer: C- Virus spreads mainly through:
A) Electricity
B) Keyboard
C) Spam links
D) Monitor
Answer: C🌐 E-Commerce
- B2C example:
A) Alibaba
B) Amazon
C) Hamrobazaar
D) School
Answer: B- C2C example:
A) Amazon
B) Bank
C) Hamrobazaar
D) Alibaba
Answer: C- M-commerce uses:
A) TV
B) Mobile phone
C) Printer
D) Scanner
Answer: B- Online payment is:
A) Cash
B) Paper-based
C) Cashless
D) Manual
Answer: C- E-commerce disadvantage:
A) Global market
B) Low cost
C) Internet dependency
D) 24/7 service
Answer: C🚀 Contemporary Technology
- Cloud computing example:
A) MS Paint
B) Google Drive
C) Calculator
D) Notepad
Answer: B- AI example:
A) Printer
B) Robotics
C) Mouse
D) Speaker
Answer: B- IoT example:
A) Typewriter
B) Smart watch
C) Book
D) Pen
Answer: B- VR is used in:
A) Banking
B) Cooking
C) Gaming
D) Typing
Answer: C- E-Governance increases:
A) Corruption
B) Transparency
C) Piracy
D) Spam
Answer: B⚖️ Ethical & Social Issues
- Cyber law introduced in Nepal:
A) 2050
B) 2061 BS
C) 2070
D) 2000
Answer: B- Hacking is:
A) Legal
B) Ethical
C) Cyber crime
D) Programming
Answer: C- Encryption converts:
A) Code to text
B) Text to code
C) Virus to data
D) Data to hardware
Answer: B- Patent protects:
A) Music
B) Art
C) Invention
D) Virus
Answer: C- Digital signature ensures:
A) Virus
B) Secure message
C) Faster typing
D) Printing
Answer: B🗄️ DBMS
- Data is:
A) Processed info
B) Raw facts
C) Organized result
D) Printed output
Answer: B- DBMS example:
A) Chrome
B) Oracle
C) Paint
D) VLC
Answer: B- Primary key:
A) Duplicate value
B) Null value
C) Unique value
D) Random value
Answer: C- Query is used to:
A) Enter data
B) Print
C) Retrieve data
D) Delete hardware
Answer: C- Table contains:
A) Fields & Records
B) Virus
C) Programs
D) Signals
Answer: A🌐 Networking
- LAN stands for:
A) Large Area
B) Local Area Network
C) Long Area
D) Line Area
Answer: B- WAN example:
A) Classroom
B) School
C) Internet
D) Lab
Answer: C- Star topology uses:
A) Trunk cable
B) Hub
C) Ring
D) Tree
Answer: B- Router finds:
A) Virus
B) Best route
C) Printer
D) Signal strength
Answer: B- MODEM converts:
A) Text
B) Voltage
C) Analog ↔ Digital
D) Virus
Answer: C- Simplex mode:
A) Two way
B) One way
C) Full duplex
D) Half duplex
Answer: B- Fibre optics uses:
A) Copper
B) Electricity
C) Light
D) Iron
Answer: C- Bus topology failure:
A) One node fails
B) Entire network fails
C) No effect
D) Faster
Answer: B- Gateway connects:
A) Same network
B) Dissimilar networks
C) Virus
D) Printer
Answer: B- Repeater:
A) Stores data
B) Amplifies signal
C) Routes data
D) Encrypts
Answer: B💻 Programming
- C developed by:
A) Bill Gates
B) Dennis Ritchie
C) Charles Babbage
D) Jobs
Answer: B- C is:
A) Case insensitive
B) Case sensitive
C) Machine language
D) Assembly
Answer: B- Modular programming:
A) Large block
B) Divides into modules
C) Deletes code
D) Encrypts code
Answer: B- Sub procedure:
A) Returns value
B) No return
C) Deletes value
D) Global
Answer: B- Function procedure:
A) No return
B) Returns value
C) Uses CALL
D) Deletes
Answer: B- Local variable:
A) Global
B) Inside procedure
C) Outside
D) Constant
Answer: B- EOF means:
A) End of File
B) End of Function
C) Enter Output
D) Error
Answer: A- MKDIR:
A) Delete file
B) Rename
C) Create directory
D) Print
Answer: C- Sequential file:
A) Random
B) Stored in order
C) Deleted
D) Virus
Answer: B- Database:
A) Program
B) Organized data
C) Virus
D) Signal
Answer: B
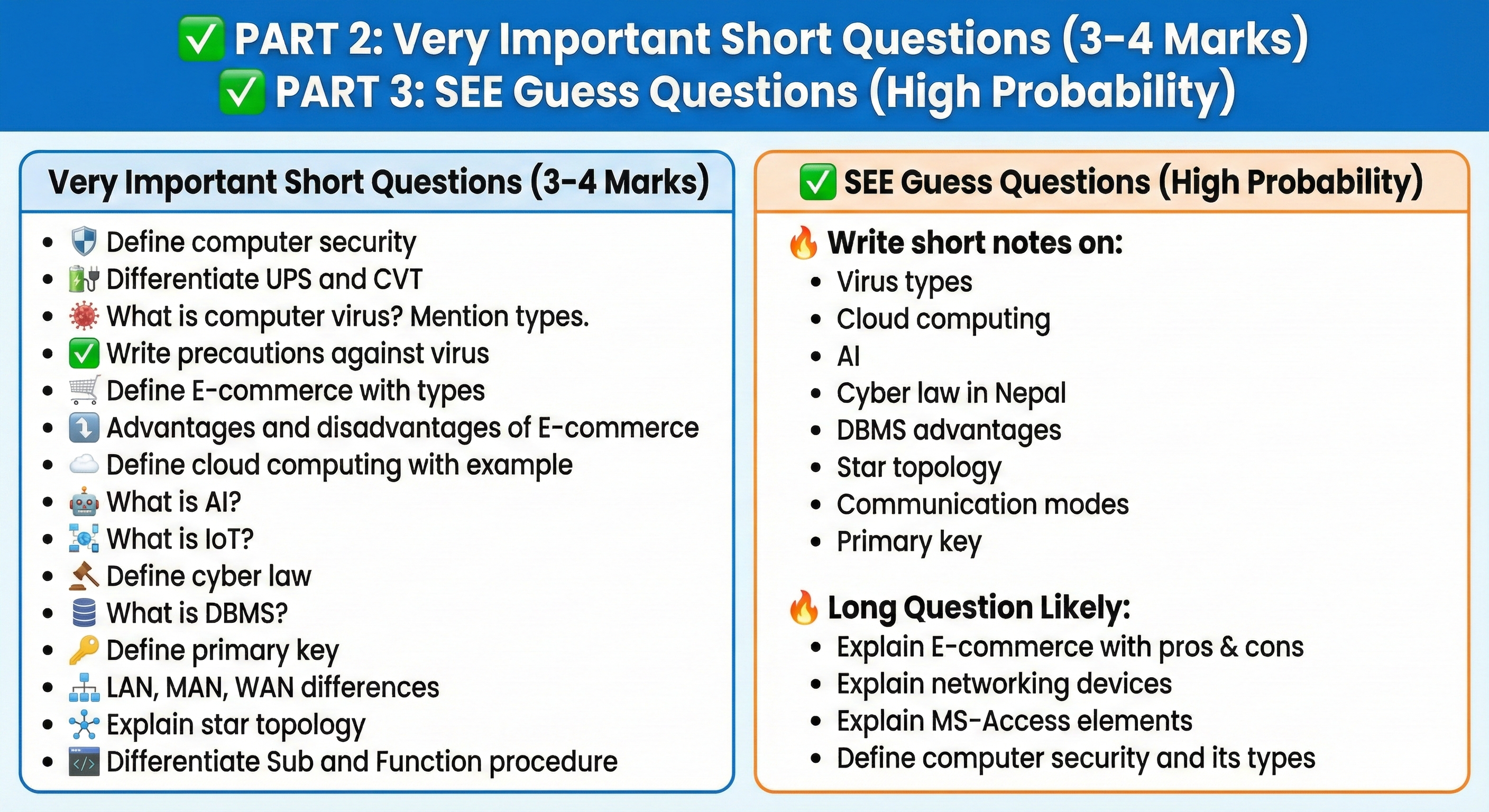
✅ PART 2: Very Important Short Questions (3–4 Marks)
- Define computer security.
- Differentiate UPS and CVT.
- What is computer virus? Mention types.
- Write precautions against virus.
- Define E-commerce with types.
- Advantages and disadvantages of E-commerce.
- Define cloud computing with example.
- What is AI?
- What is IoT?
- Define cyber law.
- What is DBMS?
- Define primary key.
- LAN, MAN, WAN differences.
- Explain star topology.
- Differentiate Sub and Function procedure.
✅ PART 3: SEE Guess Questions (High Probability)
🔥 Write short notes on:
- Virus types
- Cloud computing
- AI
- Cyber law in Nepal
- DBMS advantages
- Star topology
- Communication modes
- Primary key
🔥 Long Question Likely:
- Explain E-commerce with pros & cons
- Explain networking devices
- Explain MS-Access elements
- Define computer security and its types
✅ PART 4: Printable 5-Page Revision Sheet (Condensed Layout)
PAGE 1 → Computer Security + Virus
PAGE 2 → E-commerce + Contemporary Tech
PAGE 3 → Cyber Law + DBMS
PAGE 4 → Networking + Topologies
PAGE 5 → Programming + File Handling
✅ PART 5: ONE-PAGE ULTRA QUICK CHEAT SHEET
Computer Security = Protect data
UPS = Backup
CVT = Voltage control
Virus = Self-replicating program
Backup = Duplicate copy
B2C = Amazon
Cloud = Google Drive
AI = Robotics
IoT = Smart devices
Cyber Law = 2061 BS Nepal
DBMS = Manages database
Primary Key = Unique
LAN = Small area
WAN = Internet
Star = Hub based
Router = Best route
C = Dennis Ritchie
Sub = No return
Function = Return value