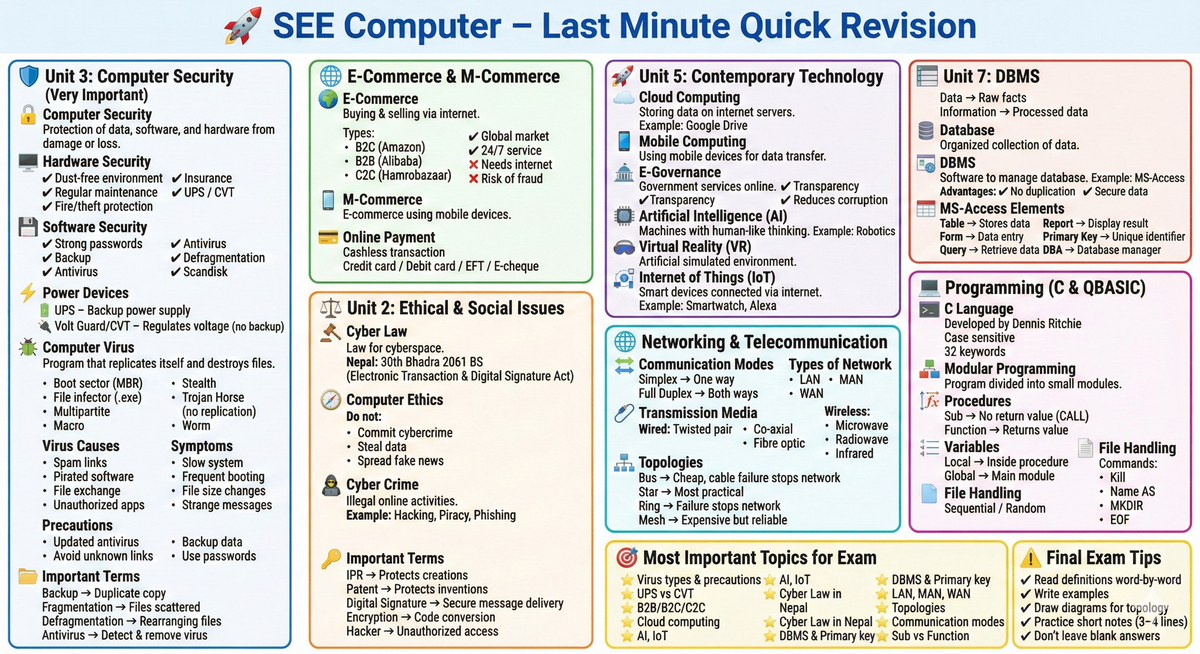
🚀 SEE Computer – Last Minute Quick Revision
🛡️ Unit 3: Computer Security (Very Important)
🔐 Computer Security
Protection of data, software, and hardware from damage or loss.
🖥️ Hardware Security
Protection from physical damage.
✔ Dust-free environment
✔ Regular maintenance
✔ Fire/theft protection
✔ Insurance
✔ UPS / CVT
💾 Software Security
Protection of data and programs.
✔ Strong passwords
✔ Backup
✔ Antivirus
✔ Defragmentation
✔ Scandisk
⚡ Power Devices
🔋 UPS – Backup power supply
🔌 Volt Guard/CVT – Regulates voltage (no backup)
🦠 Computer Virus
Program that replicates itself and destroys files.
Types:
- Boot sector (MBR)
- File infector (.exe)
- Multipartite
- Macro
- Stealth
- Trojan Horse (no replication)
- Worm
Virus Causes:
- Spam links
- Pirated software
- File exchange
- Unauthorized apps
Symptoms:
- Slow system
- Frequent booting
- File size changes
- Strange messages
Precautions:
- Updated antivirus
- Avoid unknown links
- Backup data
- Use passwords
📂 Important Terms
Backup → Duplicate copy
Fragmentation → Files scattered
Defragmentation → Rearranging files
Antivirus → Detect & remove virus
🌐 E-Commerce & M-Commerce
E-Commerce
Buying & selling via internet.
Types:
- B2C (Amazon)
- B2B (Alibaba)
- C2C (Hamrobazaar)
✔ Global market
✔ 24/7 service
❌ Needs internet
❌ Risk of fraud
M-Commerce
E-commerce using mobile devices.
Online Payment
Cashless transaction
Credit card / Debit card / EFT / E-cheque
🚀 Unit 5: Contemporary Technology
Cloud Computing
Storing data on internet servers.
Example: Google Drive
Mobile Computing
Using mobile devices for data transfer.
E-Governance
Government services online.
✔ Transparency
✔ Reduces corruption
Artificial Intelligence (AI)
Machines with human-like thinking.
Example: Robotics
Virtual Reality (VR)
Artificial simulated environment.
Internet of Things (IoT)
Smart devices connected via internet.
Example: Smartwatch, Alexa
⚖️ Unit 2: Ethical & Social Issues
Cyber Law
Law for cyberspace.
Nepal: 30th Bhadra 2061 BS
(Electronic Transaction & Digital Signature Act)
Computer Ethics
Do not:
- Commit cybercrime
- Steal data
- Spread fake news
Cyber Crime
Illegal online activities.
Example: Hacking, Piracy, Phishing
Important Terms
IPR → Protects creations
Patent → Protects inventions
Digital Signature → Secure message delivery
Encryption → Code conversion
Hacker → Unauthorized access
🗄️ Unit 7: DBMS
Data → Raw facts
Information → Processed data
Database
Organized collection of data.
DBMS
Software to manage database.
Example: MS-Access
Advantages:
✔ No duplication
✔ Secure data
✔ Data sharing
MS-Access Elements
Table → Stores data
Form → Data entry
Query → Retrieve data
Report → Display result
Primary Key → Unique identifier
DBA → Database manager
🌐 Networking & Telecommunication
Communication Modes
Simplex → One way
Half Duplex → One at a time
Full Duplex → Both ways
Types of Network
LAN
MAN
WAN
Transmission Media
Wired:
- Twisted pair
- Co-axial
- Fibre optic
Wireless:
- Microwave
- Radiowave
- Infrared
Topologies
Bus → Cheap, cable failure stops network
Star → Most practical
Ring → Failure stops network
Mesh → Expensive but reliable
Devices
Router → Best path
Repeater → Boost signal
Hub → Multi-port repeater
Bridge → Connect similar networks
Gateway → Connect different networks
MODEM → Analog ↔ Digital
💻 Programming (C & QBASIC)
C Language
- Developed by Dennis Ritchie
- Case sensitive
- 32 keywords
Modular Programming
Program divided into small modules.
Procedures
Sub → No return value (CALL)
Function → Returns value
Variables
Local → Inside procedure
Global → Main module
File Handling
Sequential / Random
Commands:
- Kill
- Name AS
- MKDIR
- EOF
🎯 Most Important Topics for Exam
⭐ Virus types & precautions
⭐ UPS vs CVT
⭐ B2B/B2C/C2C
⭐ Cloud computing
⭐ AI, IoT
⭐ Cyber Law in Nepal
⭐ DBMS & Primary key
⭐ LAN, MAN, WAN
⭐ Topologies
⭐ Communication modes
⭐ Sub vs Function
⚠ Final Exam Tips
✔ Read definitions word-by-word
✔ Write examples
✔ Draw diagrams for topology
✔ Practice short notes (3–4 lines)
✔ Don’t leave blank answers